Man vs Nature–the series–explained

Fiction by Jacqui Murray
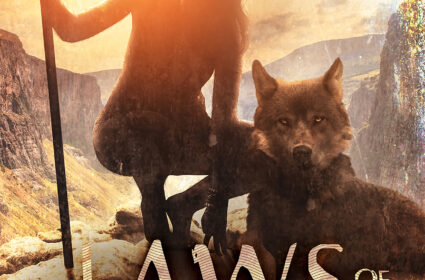
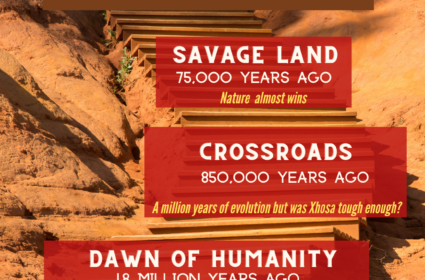
Laws of Nature
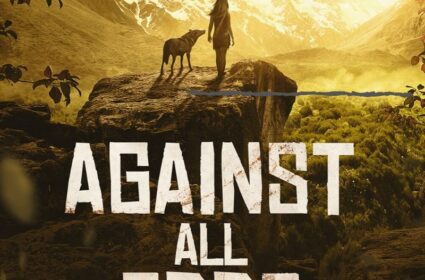
Against All Odds
The Quest for Home

Natural Selection
Survival of the Fittest

Born in a Treacherous Time

Thrillers by Jacqui Murray

Twenty-four Days
To Hunt a Sub
Nonfiction by Jacqui Murray
Building a Midshipman
Online Certificate Classes

Online Graduate Classes
Work With Me

Should You Unschool?
Is the Socratic Method Right for Your Class?
Image Copyright Do’s and Don’ts

Is Whole Brain Teaching the Right Choice?